Configure authentication and configure an identity provider on Astronomer Software
An auth system determines how users can log in to Astronomer Software. By default, Astronomer Software allows users to create an account and authenticate using one of the following methods:
- Google OAuth
- GitHub OAuth
- Local username/password
Integrating an external identity provider (IdP) greatly increases the security of your platform. When you integrate your IdP into Astronomer Software:
- Users no longer need to repeatedly login and remember credentials for their account.
- You have complete ownership over credential configuration and management on Astro.
- You can enforce multi-factor authentication (MFA) for users.
In addition to the default methods, Astronomer provides the option to integrate any IdP that follows the Open Id Connect (OIDC) protocol. This includes (but is not limited to):
- Microsoft Entra ID
- Okta
- IdPs managed through Auth0
- Amazon Cognito
After you integrate your IdP, you can invite users that already have an account on your IdP to Astronomer Software. For a more advanced integration, you can configure SCIM so that you can manage users directly from your IdP and import batches of users into Astronomer Software as Teams.
Microsoft Entra ID
Okta
Auth0
AWS Cognito
Local auth
General OIDC
Step 1: Register an application using App Registrations on Azure
-
In Microsoft Entra ID, click App registrations > New registration.
-
Complete the following sections:
- Name: Any
- Supported account types: Accounts in this organizational directory only (Astronomer only - single tenant)
- Redirect URIs:
- Web /
https://houston.BASEDOMAIN/v1/oauth/redirect/. - Web /
https://houston.BASEDOMAIN/v1/oauth/callback/.
- Web /
Replace
BASEDOMAINwith your own. For example, if your base domain isexample.com, your redirect URIs should behttps://houston.example.com/v1/oauth/redirect/andhttps://houston.example.com/v1/oauth/callback/. -
Click Register.
-
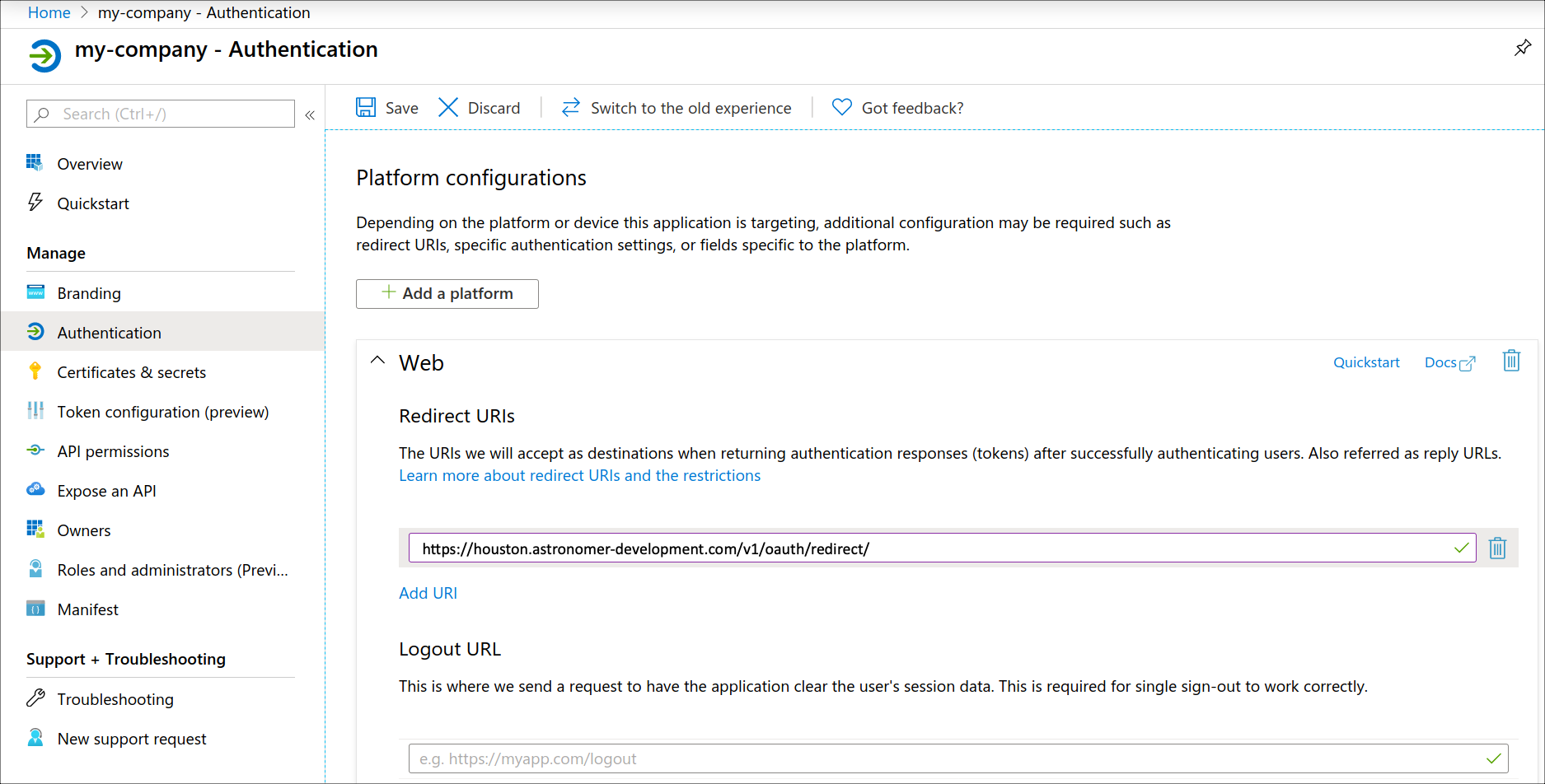
Click Authentication in the left menu.
-
In the Web area, confirm the redirect URI is correct.
-
In the Implicit grant and hybrid flows area, select Access tokens and ID tokens.
-
Click Save.
Step 2: (Optional) Create a client secret
Complete this setup only if you want to import Microsoft Entra ID groups to Astronomer Software as Teams.
-
In your Microsoft Entra ID application management left menu, click Certificates & secrets.
-
Click New client secret.
-
Enter a description in the Description field and then select an expiry period in the Expires list.
-
Click Add.
-
Copy the values in the Value and Secret ID columns.
-
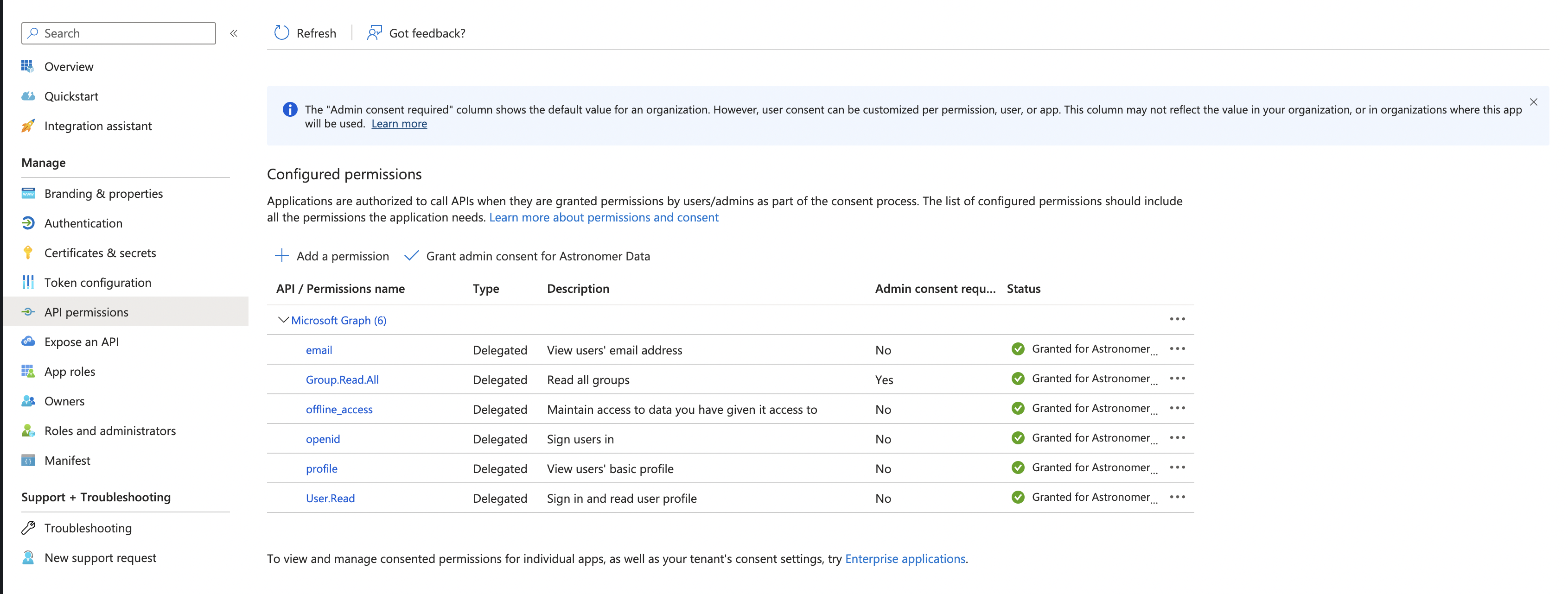
Click API permissions in the left menu.
-
Click Microsoft Graph and add the following minimum permissions for Microsoft Graph:
emailGroup.Read.AllopenidprofileUser.Read
For each of these permissions, select Grant Admin Consent for Astronomer Data. Your Microsoft Graph permissions should look similar to the following image:
-
Click Token configuration in the left menu.
-
Click Add groups claim and select the following options:
- In the Select group types to include in Access, ID, and SAML tokens area, select every option.
- In Customize token properties by type area, expand ID, Access, and SAML and then select Group ID for each type.
-
Click Add.
-
Base64 encode the client secret retrieved from Microsoft with Linux or macOS terminal with the following command:
-
Create a Kubernetes Secret in the
astronomerNamespace, or whichever Namespace where Houston is deployed, using the following YAML as an example:
- Apply the Kubernetes Secret with
kubectl apply -n astronomer -f <filename>.yaml
Step 3: Enable Microsoft Entra ID in your values.yaml file
Add the following values to your values.yaml file:
Then, push the configuration change to your platform. See Apply a config change.
Running behind an HTTPS proxy
Integrating an external identity provider with Astronomer requires that the platform’s Houston API component is able to make outbound HTTPS requests to those identity providers in order to fetch discovery documents, sign keys, and ask for user profile information upon login/signup.
If your install is configured without a direct connection to the internet you will need to configure an HTTPS proxy server for Houston.
Configure an HTTPS proxy server for Houston
To configure the proxy server used we need to set the GLOBAL_AGENT_HTTPS_PROXY Environment Variable for the Houston deployment.
To do so, add the following to the Houston section of the values.yaml file in your astronomer directory:
Then, push the configuration change to your platform as described in Apply a config change.
Configure a custom OAuth flow
Starting with Astronomer v0.27, you can set up a custom OAuth authorization flow as an alternative to Astronomer’s default implicit flow. You can customize Astronomer’s existing Okta, Google, and GitHub OAuth flows or import an entirely custom OAuth flow.
Step 1: Configure your authorization flow on Astronomer
To use a custom Oauth authorization code flow:
-
In your
values.yamlfile, set theastronomer.houston.config.auth.openidConnect.flowvalue to"code": -
Configure the section of your
values.yamlfile specific to your identity provider with each of the following values:enabled: Set this value totrueunder the section for your own identity provider.clientId: Your Client ID and Client secretdiscoveryURL: Your base Discovery URLauthUrlParams: Additional parameters to append to your discovery URL. At a minimum, you must configureaudience. Refer to your identity provider’s documentation for information on how to find this value (Auth0 maintains this information in their glossary, for example).
For example, a custom configuration of Okta might look like the following.
- Push your configuration changes to your platform as described in Apply a config change.
Step 2: Configure your identity provider
To finalize your configuration, configure the following key values in your identity provider’s settings:
- Grant Code: Set to “Code” or “Auth Code” depending on your identity provider.
- Sign-in Redirect URI: Set to
https://houston.<BASE_DOMAIN>/v1/oauth/callback/. Be sure to include the trailing/.
Step 3: Confirm your installation
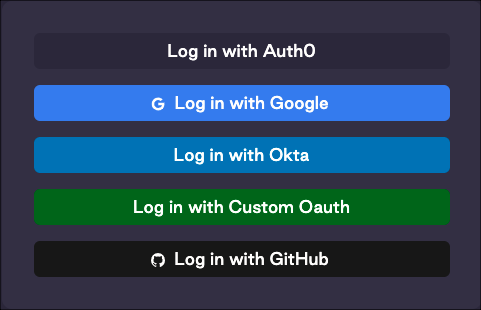
When you complete this setup, you should be able to see the differences in login flow when logging in at <BASE_DOMAIN>.astronomer.io.
If you configured a fully custom OAuth flow, you should see a new Log in with Custom Oauth button on the Astronomer login screen:
You can see the name you configured in AUTH__OPENID_CONNECT__CUSTOM__DISPLAY_NAME when authenticating using the Astro CLI.
Manage users and Teams with SCIM
Astronomer Software supports integration with the open standard System for Cross-Domain Identity Management (SCIM). Using the SCIM protocol with Astronomer Software allows you to automatically provision and deprovision users and Teams based on templates that define permission and accesses. It also centralizes user management so that you can configure Astronomer user permissions directly from your identity provider (IdP).
Okta
Microsoft Entra ID
-
In Okta Admin dashboard, go to Applications > Applications.
-
Click Browse App catalog
-
Search for
SCIM 2.0, then select the option that includes Basic Auth. The configuration page for the SCIM integration appears. -
Complete the General Settings page, then click Next.
-
Complete the Sign-On Options page and click Done.
-
Return to the Applications menu and search for the integration you just created. Click the integration to open its settings.
-
Click Provisioning, then click Configure API integration.
-
Tick the Enable API integration checkbox, then configure the following values:
- SCIM connector base URL:
https://astro-software-host/v1/scim/v2/okta - Authentication mode: Basic Auth
- Username:
<your-provisioning-account-username> - Password:
<your-provisioning-account-password>
- Username:
- SCIM connector base URL:
-
Click General, then click Edit. Give your application a name and configure any other required general settings.
-
Go to Push Groups page and create a rule for Group Push. See Group Push.
-
On the Assignments tab, ensure that the right users and groups in your org are assigned to the app integration. See Use the Assign Users to App action.
-
Follow the steps in Store and encrypt identity provider secrets to store your provisioning account credentials as a Kubernetes secret. Make sure to Base64 encode the credentials, as it is a requirement for Kubernetes secrets. This can be done using the Linux or macOS terminal with
echo '<your-provisioning-account-username>:<your-provisioning-account-password> | base64. Your secret configuration should look similar to the following: -
Add the following lines to your
values.yamlfile: -
Push the configuration change. See Apply a config change.
See Add SCIM provisioning to app integrations for more information about configuring SCIM within Okta.